Cloud storage has become ubiquitous in modern society. The most widely-used example, I think, is the one that comes prebundled with our p…
- Mainstream cloud storage providers like Google Drive and iCloud have access to users’ files, posing privacy and security risks.
- Nextcloud is the preferred secure cloud storage option, but has drawbacks like the need for technical expertise to self-host and issues with end-to-end encryption.
- Filen is a user-friendly secure cloud storage option, but has some concerns around encryption implementation.
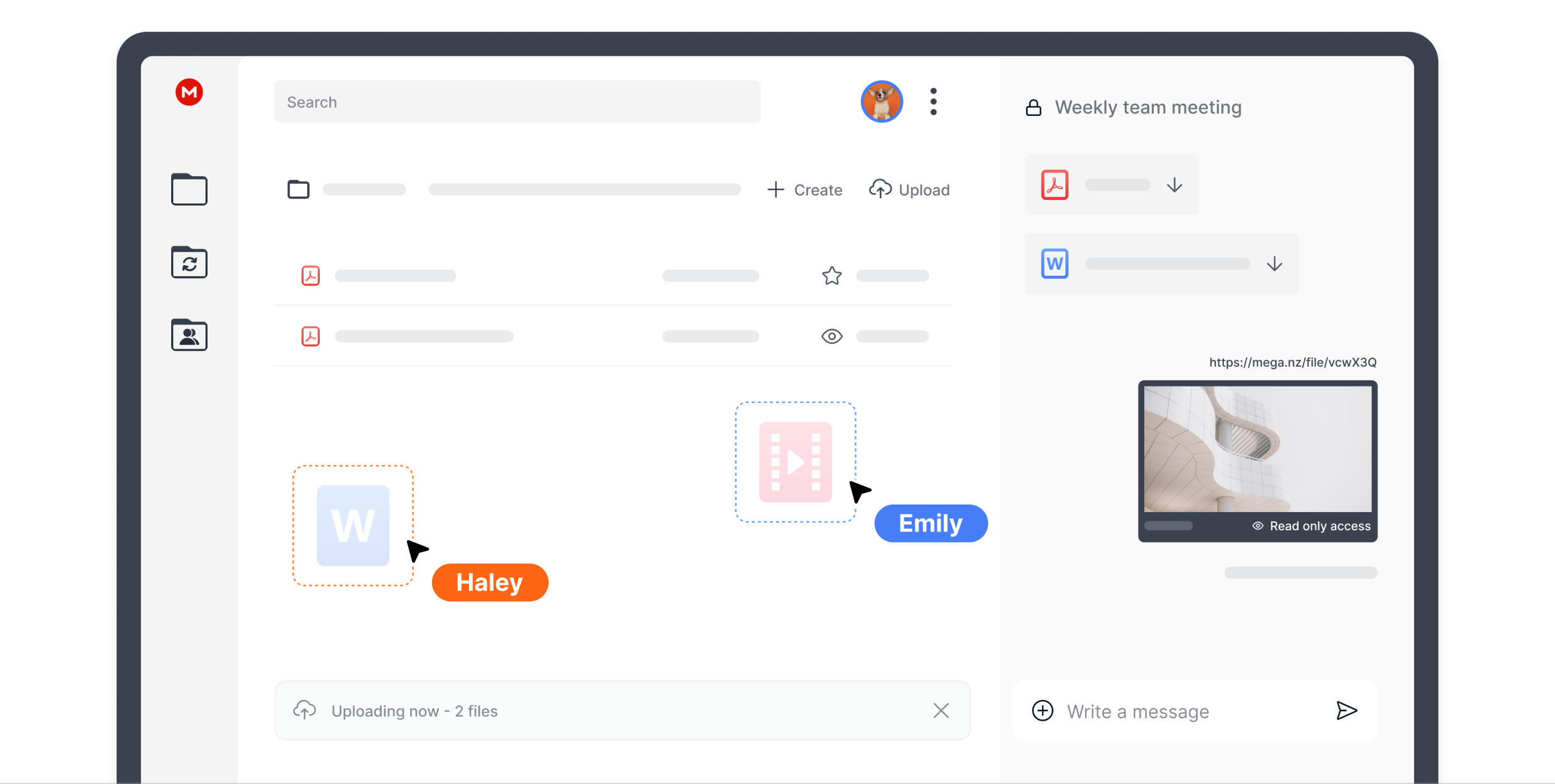
- Mega offers a large free storage plan, but has had past security issues and controversies.
- Proton’s secure cloud storage is part of their broader privacy-focused ecosystem, but has some app and feature inconsistencies.
- Cryptomator is a useful tool to add an extra layer of encryption to any cloud storage service.
- Apple’s Advanced Data Protection is a proprietary solution that lacks transparency compared to open-source alternatives.
- It’s important to weigh the risks versus benefits when choosing a cloud storage provider based on the sensitivity of the data.
- Switching to a more secure and privacy-focused cloud storage option is worthwhile, even for non-sensitive data.
- The article encourages users to take steps to improve their cloud storage privacy and security, rather than relying on mainstream providers by default.
Courtesy of Kagi’s Universal Summarizer’s Key Moments.
ssh to my bastion.
Ssh over wireguard to a container in my bastion
im gonna use my sshdick to stream some of my creamy data into your bastion
private-ish
Wow, they recommend nextcloud which doesn’t even support client- side encryption .
My recommendations are usually Tresorit, Mega, and Proton Drive. I dont know of any others that support sharing files with third parties that enforces client- side encryption on everything.
https://nextcloud.com/encryption/
End-to-end Encryption client-side is available from Nextcloud desktop client 3.0 and newer as a folder-level option to keep extremely sensitive data fully secure even in case of a full server breach. The server facilitates key exchange for syncing between devices and sharing but has Zero Knowledge, that is, never has access to any of the data or keys in unencrypted form.
It’s not a big deal if you self-host at home either. You can use SSL for the traffic and LUKS for the storage.
Again, i dont recommend nextcloud because it doesn’t encrypt everything. Same for other cloud providers. I wouldn’t use it unless everything is encrypted client-side and it cannot be turned off.
It is a big deal if you self host. If you server is owned, your data is compromised, because the server can read your data.
To be fair, if your server is taken over, there’s a good chance your other devices have been compromised first/as well, in which case you’re already in trouble.
No way. Servers are easier to compromise because they’re online all the time and by definition exposed to requests from the public internet
You can have a server without a public IP; that’s totally doable. An internal server that’s only accessible from LAN or a VPN is still a server.
Also, the majority of compromises happen because of user error (e.g., someone opens/runs the wrong thing) or an unpatched machine, not because of an exploit in server software/because the machine is always on. This is especially true in the business world where it’s often a combination of human error and the network not being segmented/ACLs not being set properly/etc (lots of cases of human error).
It’s also not that unusual for someone to keep their e.g., desktop always on or their laptop/mobile device in a low power state where it still has network activity despite being “off.”
Ente is really nice for photo storage!
Trust no one! Any cloud + rclone crypt. Solved.
How does this compare to borg ?
All storage is secure if you encrypt locally first (metadata notwithstanding). Of questionable utility for phone apps (happy to be corrected, some sort of FUSE type filesystem with cached filenames etc. could probably work), but great for offsite backups (preferably using multiple services) of critical data.
Just don’t lose the keys